Platform Identity and Access Management Architect


The Platform Identity and Access Management Architect Certification targets identity experts aiming to showcase their proficiency in evaluating identity infrastructure, crafting secure access management solutions on the Customer 360 platform, and adeptly communicating technical strategies to both business and technical audiences.
Key facts
This information will assist you if you’re interested in becoming Platform Identity and Access Management Architect certified and includes an overview of the core topics in the exam.
There are 6 areas of knowledge that are covered by the Salesforce Platform Identity and Access Management Architect certification.
Data table
| Objective | Weighting |
|---|---|
| Salesforce Identity | 12% |
| Salesforce as an Identity Provider | 15% |
| Identity Management Concepts | 17% |
| Salesforce as an Identity Provider | 17% |
| Community (Partner and Customer) | 18% |
| Accepting Third-Party Identity in Salesforce | 21% |
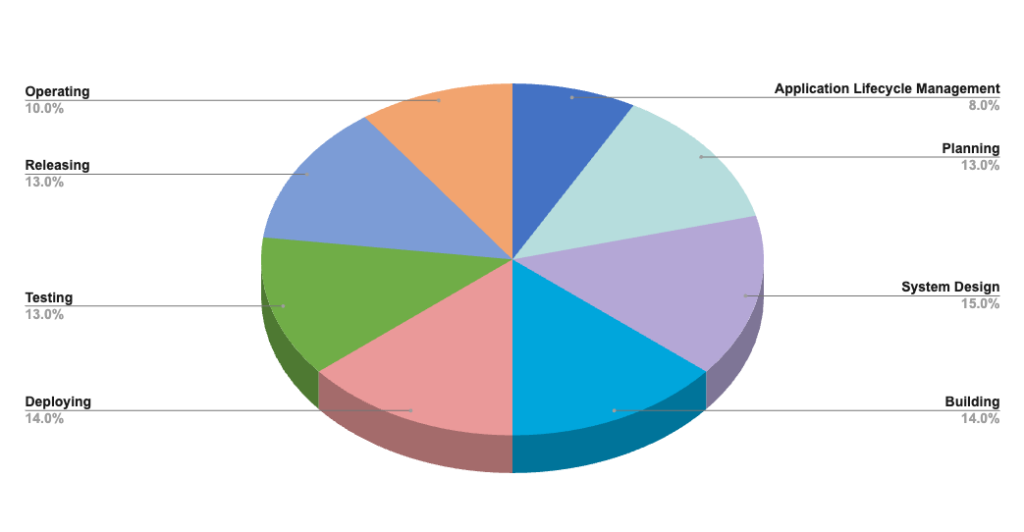
Platform Identity and Access Management Architect Topic Weighting Chart
Platform Identity and Access Management Architect
Certification Contents
The following are the core topic areas of the Platform Identity and Access Management Architect
certification and what you’re expected to know:
Identity Management Concepts
This topic includes the following objectives:
Basic Authentication is a pattern that uses username and password and is often used for basic user login through standard Salesforce login forms or API access. Multi-Factor Authentication (MFA) adds an additional security layer, requiring users to provide two or more factors when they log in. Single Sign-On (SSO) allows users to access multiple applications using a single login and one set of credentials. OAuth 2.0 authorization flows can be utilized to access protected resources. Certificate-based authentication can be configured to authenticate Salesforce users with unique digital certificates.
The core building blocks of an identity solution are authentication, authorization, and accountability. These provide a comprehensive framework for verifying user identities and controlling access to resources within Salesforce. Understanding these elements is essential for implementing effective identity and access management measures in a Salesforce instance.
Authentication verifies user identities, authorization determines their access rights, and accountability involves tracking user actions for auditing purposes. Salesforce offers a range of features to enable these building blocks, including various authentication methods, connected apps, login history, and event monitoring.
When Salesforce acts as the identity provider for an external service provider, user provisioning can be enabled for the service provider’s connected app in Salesforce. User provisioning requests can be managed, and an approval process can be defined for the UserProvisioningRequest object. Other user provisioning methods include setting up Identity Connect to push updates to Salesforce user records when user accounts are created or updated in Microsoft Active Directory (AD). Salesforce user identities can also be provisioned and managed across systems using the open standard System for Cross-Domain Identity Management (SCIM).
There are various common points of failure that may be encountered in SSO solutions. Examples include absence of My Domain, expired or revoked access token, and missing configuration such as Start URL in a service provider’s connected app.
Accepting Third-Party Identity in Salesforce
This topic includes the following objectives:

Salesforce as an Identity Provider
This topic includes the following objectives:
Moreover, various policies can be configured for a connected app, such as OAuth Policies, Session Policies, and Mobile Policies. Additional settings, like Start URL, User Provisioning, SAML, App Handler, and Digital Signatures, can be adjusted to meet specific requirements. Understanding the available scopes and configurations is essential to ensure that a connected app is configured according to the company’s business requirements.
Additional concepts include token expiration, token revocation, authorization codes, OAuth endpoints, ID tokens, and token introspection. By understanding these components, organizations can implement OAuth 2.0 flows for seamless integration with external applications and systems.

Access Management Best Practices
This topic includes the following objectives:
Salesforce Identity
This topic includes the following objectives:
Community (Partner and Customer)
This topic includes the following objectives:
Embedded Login is a feature that is used for integrating Salesforce login functionality directly into an external website, serving as a Single Sign-On (SSO) alternative. It allows users to access an Experience Cloud site using social media credentials, Login Discovery, or other custom login page type. It supports various login page implementations, including modal, pop-up, and inline login form, providing a seamless and integrated user experience.
However, it’s important to note that Embedded Login relies on third-party cookies, which are blocked or restricted in many modern browsers. This can affect the visibility and functionality of the login button if users block third-party cookies from being stored. To implement Embedded Login, it needs to be enabled for an Experience Cloud site and specific steps need to be followed to configure the login form on an external web page.